Safe, compliant end of life IT disposal – data protected, value recovered.
Through CiLifecycle, we combine rigorous data protection, environmental responsibility and value recovery.
Our secure ITAD solution ensures that every retired device is handled in accordance with regulatory and data protection standards, protecting your organisation’s data, reputation, and ESG commitments while maximising the residual value of your hardware.

From collection to erasure, destruction, recycling or remarketing. Secure ITAD covers every step of your IT asset’s final phase. Whether you’re disposing of laptops, servers, storage media or peripherals, we ensure secure, compliant and auditable disposal.
We apply industry-leading standards for data erasure, whether via verified overwriting or physical destruction, ensuring data on retired assets becomes irrecoverable, fully auditable, and compliant with legal and regulatory obligations.
Where hardware is still viable, we enable remarketing or internal redeployment, reducing e waste, supporting circular economy principles, and offering possible residual value returns. For non reusable equipment, we apply environmentally responsible recycling and certified e waste disposal methods.
Every disposed asset is logged, tracked and documented – from collection, through sanitisation/destruction, to final disposal or resale. We provide certificates of data destruction and full audit trails to support compliance, governance and ESG reporting.

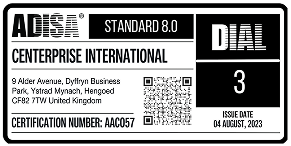
ADISA Standard 8.0

ISO 27001

ISO 14001

Supply new devices, manage their lifecycle, and automatically integrate end of life disposal with Secure ITAD.
For organisations renewing storage or backup infrastructure – combine with retirement of old storage hardware via secure disposal.
Secure retirement and disposal of network equipment, servers and infrastructure hardware at end of life. Networking & Infrastructure Decommissioning
Support your organisation’s environmental and social governance goals with responsible recycling, reuse, and carbon impact reporting.
Secure ITAD is a controlled, auditable end-of-life process for IT assets. It covers secure collection, verified data sanitisation or physical destruction, and a documented route to reuse, recycling, or remarketing, with evidence that supports compliance, governance, and ESG reporting.
Secure ITAD covers laptops, desktops, servers, storage media and peripherals. For data-bearing media, we also handle items such as hard drives, tapes, USB sticks, CDs, DVDs, mobile phones, tokens, and ID cards, with full traceability throughout processing.
We use certified data erasure methods, including verified overwriting, as well as physical destruction where required. For higher control scenarios, on-site services can include physical shredding or Blancco-certified data wiping, tailored to your media type, volume, and compliance needs.
Yes. We provide certificates of destruction and asset-level audit trails that record what was collected, how it was sanitised or destroyed, and the final outcome, supporting UK GDPR, data protection, and wider governance requirements.
Yes. We can collect securely across the UK, and internationally where applicable, with a chain of custody and secure transport. For high security requirements, on-site data destruction is available so assets do not leave your premises before data is destroyed.
Yes. Where hardware is viable, we support secure reuse routes such as internal redeployment or remarketing, helping extend asset life and recover residual value. Where appropriate, reuse can also include responsible second-life outcomes through programmes designed to deliver social benefit.
Non-reusable equipment is processed through responsible, compliant recycling aligned with environmental regulations, supported by environmental management certification. For WEEE, we ensure secure handling of any data-bearing components, use carefully selected downstream partners, and provide audit reports and certificates as proof of compliant disposal.
Secure ITAD can be built into refresh and lifecycle planning so end-of-use collection, asset tracking, and secure disposal happen as part of a repeatable programme. Device as a Service and lifecycle management can also connect procurement, deployment, ongoing management, and end-of-life disposal under one coordinated approach with documentation and reporting throughout.